Security researchers uncovered a supply chain attack targeting macOS developers that compromised thousands of credentials. The campaign, dubbed “s1ngularity,” exploited versions 20.9.0 to 21.8.0 of Nx, a popular open-source build framework, according to analysis from GitGuardian.
The breach highlights the growing overlap between macOS attacks and the broader ecosystem of AI and software development tools, raising concerns about the integrity of developer pipelines worldwide.
How the Attack Worked
GitGuardian reported that attackers tampered with the Nx package to insert malicious code directly into builds. When macOS developers installed or updated the affected versions, the backdoored package harvested authentication tokens and credentials from their systems.
The stolen data included:
- GitHub personal access tokens
- npm credentials
- SSH keys
- Environment variables containing API keys
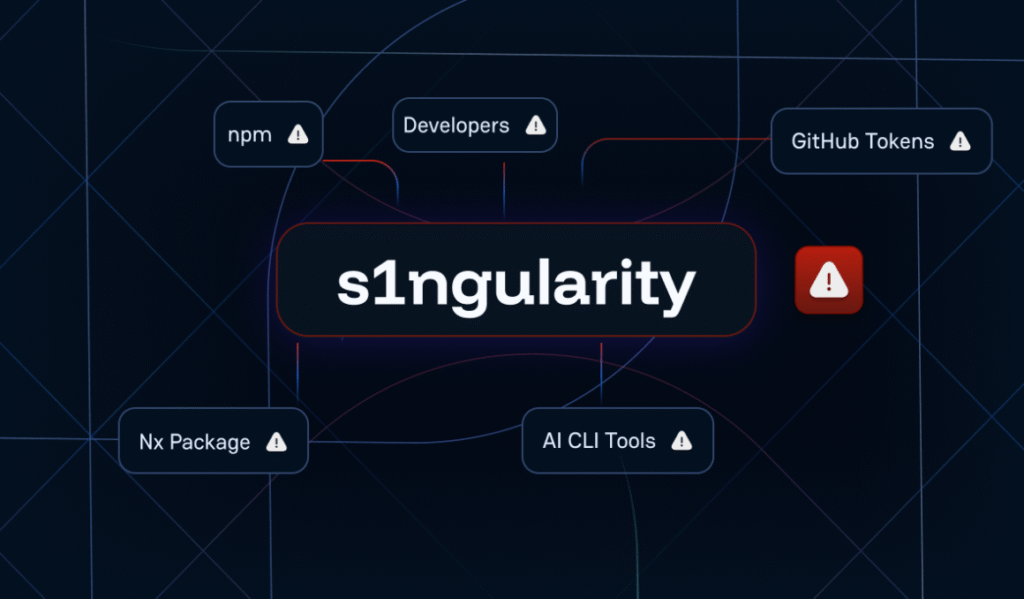
Attack Explained (Source: GitGaurdian)
This information was then exfiltrated to attacker-controlled servers, enabling lateral access to private repositories, AI development environments, and cloud platforms.
Targets and Exposure
Researchers estimate that thousands of developers fell victim during the attack window. Since Nx is widely used in enterprise and AI projects, the scope of stolen credentials could extend far beyond individual accounts.
GitGuardian’s team warned that the incident demonstrates how quickly a compromised open-source component can ripple across the software supply chain. Even organizations outside the immediate blast radius could inherit backdoored code through dependencies.
Why macOS Was a Key Target
While supply chain compromises often focus on Windows or Linux ecosystems, this attack specifically targeted macOS developers. Analysts believe the attackers aimed to exploit the rapid adoption of Apple Silicon and macOS-based AI development environments.
macOS machines are increasingly favored by developers working with machine learning frameworks, and by targeting them, attackers maximize the chance of stealing high-value API keys linked to cloud AI services.
GitGuardian’s Findings
GitGuardian’s analysis showed that the injected payload was designed to operate quietly, with minimal disruption to workflows. By blending into routine package installation, the malware harvested credentials without triggering obvious alerts.
The firm emphasized that while the campaign appeared highly automated, its execution showed precision:
- Targeting a specific version range of Nx.
- Filtering credentials for platforms most valuable to attackers.
- Leveraging macOS-specific file paths for maximum reach.
The Road Ahead
GitGuardian continues to investigate the scope of the s1ngularity campaign. While no attribution has been made, the attack’s sophistication suggests a well-resourced group with interest in AI-driven environments.
For now, the incident reinforces a critical lesson: even widely trusted developer tools can be weaponized in supply chain attacks. Security experts warn that organizations must treat dependency management with the same scrutiny as endpoint security, especially in environments where macOS and AI pipelines intersect.